 Ten days. That’s how long the computer systems were down at MGM Resorts in Las Vegas recently after a ransomware attack crippled operations at the casino and hotel giant. Around the same time, MGM’s competitor in the desert, Caesar’s, reportedly paid millions in ransom money to mitigate a similar malicious hit to its systems and data.
Ten days. That’s how long the computer systems were down at MGM Resorts in Las Vegas recently after a ransomware attack crippled operations at the casino and hotel giant. Around the same time, MGM’s competitor in the desert, Caesar’s, reportedly paid millions in ransom money to mitigate a similar malicious hit to its systems and data.
What a mess. By all accounts, the attackers used social engineering techniques to gain access to these mammoth casino networks. In other words, they manipulated humans. In one case, the weak link was an internal help desk employee fooled by the hackers; in the other it was a third-party IT provider on contract. Either way, both incidents further demonstrate the sophistication of today’s cybersecurity bad guys. They also underscore the immense need for cybersecurity skills education not only at the layperson user level, but among the professionals who supposedly know better.
Cybersecurity Challenge: The People Factor
Skills gaps and user education are among two of the main items outlined by companies as cybersecurity challenges in CompTIA’s recently released State of Cybersecurity 2024 research. The broader report, which focuses on the businesses using technology today, provides a deep dive into the recent trends across this vast discipline that impacts all corners of a company’s operations.
At a high level, cybersecurity-related data collected for the report fits into four primary topic areas, or what CompTIA has identified as the “Four Ps.” These are policy, process, people and products. In this article, we’ll focus on the people bucket, specifically the ways in which companies are using third-party technology firms and/or experts—MSPs, MSSPs, solution providers, consultants, etc.—to help them address all or some of their cybersecurity needs.
Cybersecurity-Savvy Third-Party Providers
We all know that when it comes to general technology needs, companies large and small have been engaging with third-party providers for decades. Whether it’s for procurement and implementation/deployment of tech products, project work, IT consulting services or the ongoing relationship of managed services, the end user to IT provider engagement is there, though the scope and scale of it can, and often does, vary widely.
Cybersecurity services have often been part of these transactions, typically around antivirus, firewall, patch management and other fundamental software tool deployments needed to help protect devices and networks. But today’s cybersecurity needs run far beyond those basics. And that means that outside providers need to up their game as more is expected of them.
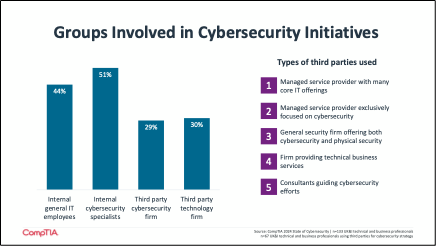
Nearly one third of companies surveyed said they use third-party firms with a dedicated cybersecurity practice, and approximately the same number use third-party firms that provide a variety of technology services. There obviously may be overlap between these two, as companies use a variety of partners and technology providers to build their overall technology footprint and to complement internal resources. A general-purpose MSP might also offer a level of cybersecurity services that meets the needs of most companies. Other customers, however, might need a higher-level of dedicated cybersecurity skill for their business, and thus seek out third parties that meet that bar.
Based on this year’s research, customers today are looking for providers that have real-time insights into the cybersecurity threat landscape, which can encompass ransomware, social engineering, malware releases and other more sophisticated attack types on the horizon.
A lens into the threat landscape is often difficult for an internal IT department to maintain itself, as it is tied up juggling day-to-day mandates and projects. In these cases, an MSP or solution provider with access to an information sharing and analysis organization (ISAO) can be invaluable. An ISAO is a community of practitioners and cybersecurity experts that collaborates to identify and disseminate information about cybersecurity threats. The information they gather is shared with businesses, governments and other entities that participate in their services.
Related: Learn more about the CompTIA ISAO
Companies today also want providers that specialize in effective mitigation and recovery strategies in the event of a breach or other incident. These fix-it services are essential and should be ironed out contractually ahead of any engagement. Part of mitigation is often user education services, which third parties can also offer in terms of training their customer’s staff on cybersecurity best practices, new tools, etc. Finally, some customers are also looking for third parties with expertise in cyber insurance, a burgeoning area of specialty for channel firms looking to stand out.
It's a long list of needs, to be sure. In order to deliver for their customers, channel firms will need to address their own skills gaps across the complex cybersecurity discipline. Hiring the right individuals, training and upskilling, and partnering with other solution providers to fill skills gaps should be high on the to-do list now and for the coming year.

 Add CompTIA to your favorite RSS reader
Add CompTIA to your favorite RSS reader

.png?sfvrsn=14e9862c_2)